Field of the Disclosure
Background
It is often difficult to raise the budget of a large venture such as a merger, an acquisition, a securities private placement or an initial public offering (IPO). In addition to significant cost, it monopolizes a significant portion of the company’s resources and the management’s attention. That is why it is not uncommon that during the venture capitalization (e.g. IPO) process, the performance of the company is heavily impacted. Hence, there may be an additional need for funding, if only to offset the poor sales performance due to the effort of the venture capitalization or IPO process.
The risk linked to a transaction financing investment is directly linked to the probability of the transaction being successful. Therefore, as a rule of thumb, we can say that the transaction financing investment risk is directly linked to the quality of the agreements binding the parties to the transaction and to these parties’ willingness to execute the transaction properly.
Financing ventures are guided by considerations of two different entities, investors and entrepreneurs. The investor’s viewpoint is how to invest for a short period of time and make a significant profit. The entrepreneur’s or the company’s point of view is how to finance a large transaction and get rid of the investors immediately afterwards. More often than not, when acquiring or merging, it is possible to use the cash of the target company to pay off investors. Thus, transaction financing answers both these needs allowing the investor to make a quick profit in case of successful transaction. However, depletion of cash or adding debt load to the new venture to finance the acquisition can hinder growth of the venture after the financial transaction. In IPOs, there is no cash to pay off investors, so the investors cannot exit quickly.
On the other hand, it is appropriate to differentiate, in the total cost of an IPO or other venture capitalization, the costs that must be borne by the future company issuing shares before trading the IPO process, called “Upfront” or “Pre-Cash” (fees of lawyers, etc.), from those which will be supported at the end of the IPO by the raised funds, “Post-Cash” (commissions of Brokers or Investment Banks, etc.).
Financing could be structured as loans or bond issues. However, under many jurisdictions, loans are limited to a certain interest rate percentage, called the usury rate, generally less or far less than 25%. For example in Switzerland, the federal law limits this usury rate at 15% and makes any interest rate set above that limit unlawful and thus, not payable. Bond issues may be limited by market rates and bond ratings assigned by market assessment firms that assign risk valuations to the issue based on perceived success of the venture to be funded. Further, loans and bonds are typically structured to provide payments to investors at defined payment schedules.
Often, investors want a higher return on their investment, because any transaction financing investment represents a significant degree of risk at least from a market perception standpoint. They may also wish to recover their investment faster than loans or bonds.
Therefore, it is desirable to develop new systems and methods for raising venture capital.
Summary
Provided herein is a system for financing a venture comprising an incubator financial firm configured to manage activities related to raising funds for the venture against an equity participation and a put option on this equity participation to the issuer; and a special vehicle firm that holds all assets of the entity seeking financing; wherein the incubator financial firm defines an investor offering to raise funds from investors against a share of the capital prior to the IPO and a pro rata share of the raised funds payable after the IPO.
Also provided herein is a method for financing a venture comprising establishing an incubator financial firm configured to manage activities related to raising funds for the venture against an equity participation and a put option on this equity participation to the issuer, wherein the incubator financial firm defines an investor offering to raise funds from investors against a share of the capital prior to the IPO and a pro rata share of the raised funds payable after the IPO; and establishing a special vehicle firm that holds all assets of the entity seeking financing.
Also provided is a company for financing a venture comprising a financial firm configured to manage activities related to raising funds for the venture against an equity participation and a put option on this equity participation to the issuer.
An embodiment of the company is wherein the financial firm defines an investor offering to raise funds from investors against a share of the capital prior to the IPO and a pro rata share of the raised funds payable after the IPO.
Also provided is a method for providing an equity security, the method comprising: defining an offering for sale of investment shares in a venture; receiving bids from investors for purchase of the investment shares; accepting the bids from investors; tracking revenue associated with the sale of the investment shares; and paying parties a portion of the revenue as it is received.
Also provided is a system comprising a computerized system with hardware and specialized software components for developing, executing and administering sale of securities, the system comprising a non-transitory computer readable storage medium comprising a plurality of computer readable instructions embodied thereon which, when executed by the computerized system, causes the computerized system to: define an offering for sale of investment shares in a venture; receive bids from investors for purchase of the investment shares; accept the bids from investors; track revenue associated with the sale of the investment shares; and pay parties a portion of the revenue as it is received.
Also provided is a non-transitory computer readable storage medium comprising a plurality of computer readable instructions embodied thereon wherein the instructions, when executed by a computerized system with hardware and specialized software components for developing, executing and administering intellectual property securities, cause the computerized system to: define an offering for sale of investment shares in a venture; receive bids from investors for purchase of the investment shares; accept the bids from investors; track revenue associated with the sale of the investment shares; and pay parties a portion of the revenue as it is received.
Brief Description of the Drawings
The disclosed aspects will hereinafter be described in conjunction with the appended drawings, provided to illustrate and not to limit the disclosed aspects, wherein like designations denote like elements.
FIG. 1 depicts a schematic chart of incubator and SPV firms related to a venture capitalization according to an exemplary embodiment of the disclosed subject matter.
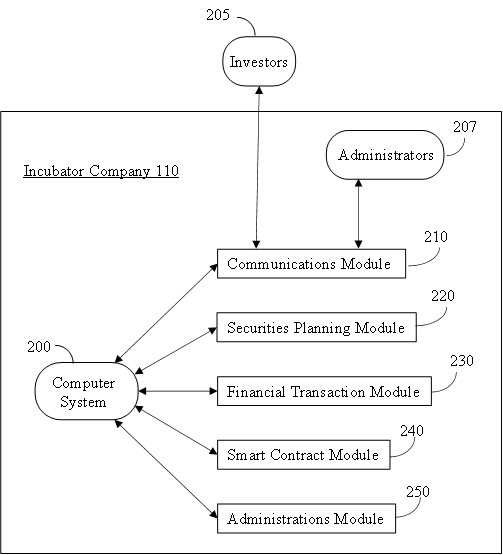
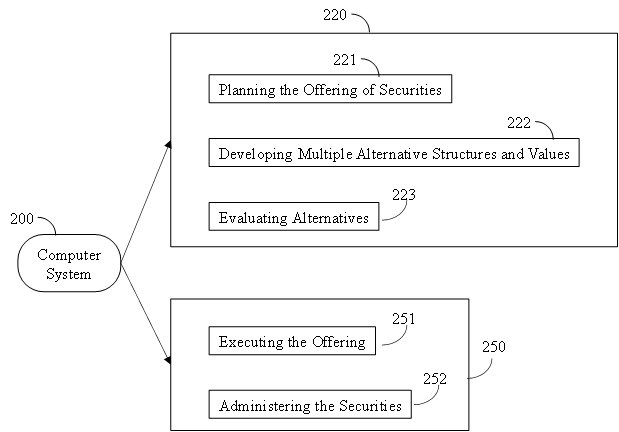
FIG. 2A and 2B depict schematic functional diagrams of a computer system relating to planning and developing securities, modeling and evaluating alternatives, as well as executing and administering an offering for sale of securities according to an exemplary embodiment of the disclosed subject matter.
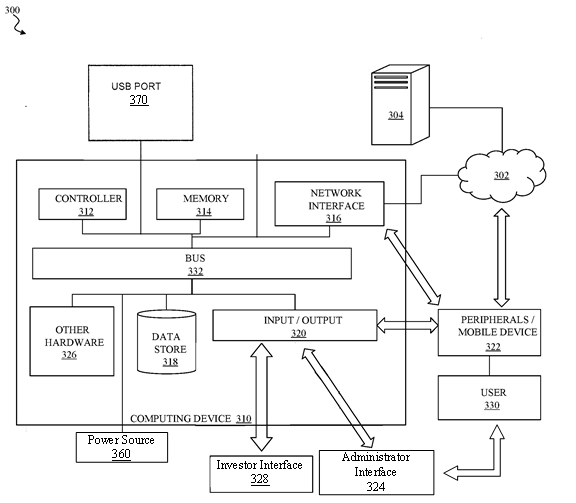
FIG. 3 depicts a functional diagram of components of a computer system according to an exemplary embodiment of the disclosed subject matter.
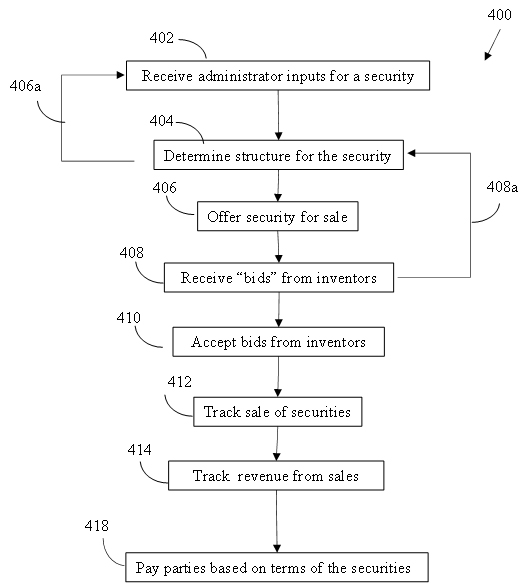
FIG. 4 shows a process flow diagram for defining, offering for sale and administering a security by an incubator company according to an embodiment of the disclosed subject matter.
Detailed Description of the Disclosed Subject Matter
In accordance with various embodiments of the invention, and as shown in the figures, various systems and methods are disclosed which generally provide a platform for financing a venture comprising an incubator financial firm configured to manage activities related to raising funds for the venture against an equity participation and a put option on this equity participation to the issuer; and a special vehicle firm that holds substantially all tangible and intangible assets of the entity seeking financing.
As illustrated in Figure 1, an entity or company 100 seeking venture capital funding may set up an Incubator company 110 to manage aspects of the venture capitalization, including organizing information roadshows to exchange information with potential investors, prepares disclosures, defines offerings to investors, conducts sale of securities, and manage financials, including receiving payments for securities from inventors 130 and distributing payouts to parties including company 100, investors wishing to exit the securities 140. The incubator company 110 retains a portion of the income from the sale as payment for its activities. A special purpose vehicle (SPV) company 120 is also set up to hold tangible and intangible assets related to current ventures and manage current operations. Company 100 retains control of the SPV company 120 through the financing process, such as by retaining a portion of shares in the SPV while the remainder of the shares in the SPV are sold to investors. After the venture capitalization is complete, the Incubator company 110 is dissolved or otherwise severed from company 100.
As used herein, a fundraising Incubator is a company financing corporate transactions such as a merger, an acquisition, a securities private placement or an initial public offering (IPO) against an equity participation and a put option on this equity participation to the issuer itself. The put option, issued by the same issuer as the equity participation, ensures the investor that, in case of success of the transaction, the investor can resell this participation to the issuer immediately after.
The function of the Incubator is to manage aspects of the venture capitalization process, while the management and structure of the entity seeking funding can continue to manage aspects related to its normal corporate and entrepreneurial functions including development, production and sale of commercial products to consumers. Separation of the entity’s normal functions from aspects related to the venture capitalization is accomplished by formation of a special purpose vehicle.
As used herein, a special purpose vehicle (SPV) company is an industrial and commercial company that holds all assets of the company or group seeking IPO financing consolidated together. Assets held by the SPV are related to the commercial offerings of the company or group and include for example, intellectual property and know-how, tangible assets including infrastructure, equipment, goods for manufacturing product(s), inventory of product(s) for sale etc., and human assets including employees and management personnel. Although this is not an absolute obligation, it is desirable for the future SPV issuer to remain financially, commercially and in every sense of the word credible in front of the financial market. This aspect should be studied case by case as part of the definition of the IPO or other venture offering. In some embodiments, when a known group or entity has a subsidiary bearing all or part of its name, for example; BOUYGUES Telecom or PEUGEOT Leasing, the SPV may hold assets from the subsidiary while not holding assets within a parent entity outside of the subsidiary.
The process of organizing an IPO, or other venture capitalization vehicle comprises the following steps.
- An IPO Incubator Company, or “Incubator” is incorporated, for example in the State of Delaware in the United States of America. It can be a traditional financial company that, depending on its structure, may or may not be required to register with the Securities and Exchange Commission (SEC) as a subject of the 1940 Investment Company Act.
- A special vehicle (“SPV”) company is incorporated, such as in Delaware, USA. It is an industrial and commercial company wherein all assets of the company or group seeking IPO financing are consolidated together. It could be seen as a holding company; however, it is desirable to treat the SPV as a fully operational entity and not a holding company, which can result in a significant devaluation when a listed company is perceived by the market as a “Holding”.
- The Incubator’s legal team prepares a “Regulation A+” disclosure document for the Incubator. Since this document is very similar from one time to another, the cost of this operation should decrease significantly over time as the Incubator organizes more venture financing vehicles. This disclosure document states to the investor that Incubator is an investment company that finances IPOs of any size, against a share of the capital prior to the IPO and a pro rata share of the raised funds payable after the IPO.
The Regulation A+ document offers the investor three ways out of investment:- The investor can sell Incubator shares at the time of the IPO; or
- The investor can convert Incubator actions into SPV actions after the Incubator IPO and before the start of the SPV IPO process; or
- Incubator buys back the investor’s shares after (its) Incubator IPO.
- Incubator files with the Securities and Exchange Commission (SEC) for registration and listing on a (US) stock market such as the NASDAQ or New York Stock Exchange.
- The SEC reviews the file and sends its comments, questions and possible objections to Incubator.
- Meanwhile, the Incubator and the investment bank or investment bank syndicate that distributes the Incubator’s shares are holding roadshows to promote the stock on the market and to collect Incubator’s share “orders”. During this period, legally, each market player is not allowed to buy the shares, but can only express interest and quantify the amount s/he is willing to invest. In practical terms, a buyer who expresses an interest in a quantity of shares and then withdraws would lose any credibility on the market and would be unable to continue trading in other IPOs.
A Roadshow is a presentation organized by an issuer of securities and the syndicate of brokers and investment banks underwriting an issue of securities, aiming at presenting to investors an opportunity of investment.It may take place in a hotel, a convention center, a bank or other prestigious place under various circumstances such as a Private Offering of equity or debt securities, an Initial Public Offering (IPO), a Secondary Public Offering or a Non Deal Presentation. In other embodiments, the roadshow may be virtual, presented via electronic media such as via the Internet or a limited access network (e.g. in a webcast). During the roadshow, the management of a company issuing securities or doing an Initial Public Offering (IPO) gives presentations to analysts, fund managers, potential investors and their financial advisors.
The roadshow is intended to generate excitement and interest in the issue or IPO, and is often critical to the success of the offering. The roadshow may move across many locations that are scheduled in advance and completed over a specific time period to inform and engage multiple potential investors. Roadshows may be sometimes be limited to one country but usually include several international stops. Within the United States, some common destinations include New York City, Chicago, Los Angeles, Miami and Denver.
Roadshow events may attract hundreds of prospective buyers interested in learning more about the offering. The events may include multimedia presentations and question-and-answer sessions with several of the company’s officers present. Many companies take advantage of the internet and post versions of road show presentations online. In addition to the larger road show events, companies may also hold smaller, private meetings in the months and weeks preceding the offering.
Roadshows cover a variety of topics including the company’s history and future plans for growth. Information about the company’s current assets, whether tangible or intangible, can be presented, as well as a sales pitch regarding the upcoming offering.
Aside from providing information regarding the offering, the roadshow allows the company the opportunity to answer questions that may be posed by skeptics in the marketplace or during due diligence meetings. It provides a forum where the company can communicate directly with potential stakeholders to address any potential concerns.
The underwriters also use information gathered from investors to complete the book-building process, which involves gathering prices potential investors are willing to pay for the offering.
Once the road show activity is completed, the final prospectus is created and distributed to potential investors. This prospectus is also filed with the U.S. Securities and Exchange Commission (SEC).
An initial price for the offering is set based on the information gathered during the book-building process, and the IPO date is solidified.
A non-deal roadshow occurs when executives hold discussions with current and potential investors but nothing is offered for sale. A roadshow provides an introduction of the offering to potential investors and was considered a key non-financial factor in buying decisions made by 82% of institutional investors in regards to IPOs in a 2014 study by Ernst & Young.
- At the end of this process (points 3 above to 6 above) iteratively, the SEC gives the Incubator’s legal team the quotation authorization.
- Incubator can therefore register with a US stock market, such as the NASDAQ. In the rare case of multiple listings, Incubator may also register with foreign stock exchanges.
- Incubator launches the IPO.
- Once the funds are raised, in accordance with the use of the product stipulated by the Regulation A+ Disclosure Document, Incubator makes at least the following payments:
- A payment to the investment bank’s account to pay the brokerage commission if it has not been deducted before the funds were sent to Incubator.
- A payment to the SPV account to secure SPV funding.
- Payment of SPV’s IPO fees and expenses to the lawyers’ account.
- The payment of a success bonus on the account of the lawyers according to the prescribed procedures.
- The payment to the financier of the Incubator IPO.
- SPV receives from Incubator the budget necessary to carry out its IPO.
- SPV’s legal team drafts a “Regulation S-1” disclosure document for the SPV.
- SPV’s legal team prepares the SPV registration file with the SEC in Form S-1 and the due diligence file. This is much longer than the Regulation A+ form prepared for Incubator. It should be noted that the Regulation A+ form is a short form because it seeks a partial exemption from registration, while the S-1 form is a complete record including all significant transactions carried out by the issuer in the last five or ten years, according to the case. The issuer cannot begin this full registration process until it has two full accounting years and a number of financial conditions completed.
- This document offers the investor three ways out of investment:
- The Investor sells SPV shares at the time of the IPO; or
- The SPV buys back the Investor’s shares after Incubator’s IPO; or
- Finally, the Investor does not wish to leave and remains a shareholder of the SPV.
- SPV files its prospectus with the SEC in order to be able to register there and obtain the listing of its shares on a US stock market.
- The SEC reviews the SPV’s file and sends its comments, questions and possible objections to SPV.
- Meanwhile, SPV and the investment bank or investment bank syndicate that distributes its shares organize roadshows to promote the security on the market and to collect SPV’s “orders” for shares. During this period, legally, each market player is not allowed to buy the shares, but can only express interest and quantify the amount s/he is willing to invest. In practical terms, a buyer who expresses an interest in a quantity of shares and then withdraws would lose any credibility on the market and would be unable to continue trading other IPOs.
As shown in FIG. 2A, a computer system 200 is the core element of the securities architecture within the incubator company 110, receiving, generating, storing, integrating and coordinating data required for defining the securities, receiving investment payments from a plurality of investors 205, optionally generating smart contracts among investors and the company, determining revenues related to the securities and administering payouts to parties. The computer system is further provided with at least one processor and into which is loaded software components for receiving informational inputs from the plurality of potential investors via communications module or interface 210.
Block 210 represents a communication module, which manages inputs from investors and transmits outputs to the investors. Inputs from investors include investing information, investor interest in the potential offering, investor identity, designation of a payment vehicle or digital “wallet”, such as a bank account, credit or debit account, including credit or debit cards issued by a financial institution, Venmo or Pay Pal® apps, etc. Communications module 210 may also be used by administrator(s) 207 within the incubator company 110 of the computer system to communicate with the system. Administrator(s) may provide inputs to the system to maintain and manage the system to make sure it is operating correctly. In embodiments, the administrator(s) 207 may also provide information from the sellers (e.g. company 100), brokers, investment banks, underwriters, etc., risks assessments, projected revenue streams, etc.
In block 220, the system includes a securities planning module in which the securities are defined, as described in greater detail in regard to Figure 2B.
Block 230 comprises the financial transactions module that manages payments from investors to cover their bids, payments to parties and collection of transaction fees. In embodiments, once a bid is accepted, the financial transactions module may withdraw the bid amounts plus transaction fees from investors’ payment vehicles in response to acceptance of bids by the computer system. Block 230 also disburses payments to the parties based on the terms of the securities.
In embodiments, the securities may be offered in the form of a smart contract, described in greater detail below. In block 240, the smart contract module executes smart contracts by generating data blocks defining the securities, including all terms and conditions binding on the investors and the company such as purchase prices, percentages of the assets represented by the securities, etc.
Block 250 shows the securities administration module, which executes and administers the securities.
As shown in Figure 2B, block 220 comprises aspects of defining the security offerings.
In block 221, planning the offering of securities includes establishing the target amount of capital to be raised. Guided by inputs from administrator(s) of the system representing the seller, bank, broker, underwriter and/or other financial institutions, the system conducts feasibility studies for offering intellectual properties to define the structure of the offering. Inputs may also include information from potential investor gathered in roadshows, etc. The offering planning includes specific variables to be included, ranges of acceptable values for each variable, and terms and conditions to be included in the offering.
In block 222, the system models and projects multiple values of individual variables and combinations of multiple sets of variables, such as time series projections and economic modeling of interaction between variables.
In block 223, the system evaluates alternatives by reviewing results of modeling and projections. Selecting one or more sets of variables that meet targets will be used to refine the structure and value of variables and terms and conditions for price categories of the shares. Additional modeling and projections may be required to define a preferred set of values for the variables and terms and conditions for inclusion in the offering of securities in the price categories of the shares.
Figure 2B also shows block 250 comprising aspects of administering the security offerings.
In block 251, the system executes the offering of the securities. The price and content of the individual shares are established. Technical and legal details are finalized required disclosures are prepared, and the securities are brought to market. The system receives and accepts bids for shares in the security from at least one investor, tracks progress of sales of shares in the security, and closes sales when target values are met. The system may also receive sell orders from holders of shares and sell them to new investors.
Block 251 may comprise an order creation module. In general, the order creation module may have two modes of functionality. In a first mode, the order creation module permits an investor to express interest in pre-offering activities and provide that information to the securities. .In a second mode, the order creation module receives and processes bids from investors after the offering is listed.
In block 252, the system administers the securities (shares) in the offering. It maintains detailed and current records of individual investor accounts as required for periodic and cumulative payments, tax treatment, benefits, reports and other purposes. It maintains required and useful records related to financial analysis and financial reports of investors, brokers, and other involved parties.
In embodiments, the offering, sale and administration of the securities may be conducted as a smart contract.
A smart contract is a computer application simulating the operation of a contract. It is a computer program or a transaction protocol which is intended to automatically execute, control or document legally relevant events and actions according to the terms of a contract or an agreement between or among parties. The objectives of smart contracts are the reduction of need in trusted intermediators, arbitrations and enforcement costs, fraud losses, as well as the reduction of malicious and accidental exceptions. The smart contract is stored on a blockchain that runs when predetermined conditions are met. They may be used to automate the execution of an agreement so that all participants can be immediately certain of the outcome, without any intermediary’s involvement or time loss.
The reliability of the smart contract comes from its automaticity which gives it a power of execution unmatched to date.
A smart contract also can be regarded as a secured stored procedure as its execution and codified effects like the transfer of some value between parties are strictly enforced and cannot be manipulated, after a transaction with specific contract details is stored into a blockchain or distributed ledger. That is because the actual execution of contracts is controlled and audited by the platform, not by any arbitrary server-side programs connecting to the platform. Smart contracts are particularly useful for managing exchanges of virtual financial or value assets, where no tangible materials need to be moved.
The smart contract preferably is structured to adhere to the basic rules of prudence in a transaction financing investment including the following:
- Having a commitment from both parties to the transaction provides the safest conditions to the investment. Commonly, a transaction financing agreement is entered into between one party to the transaction and the representative of the investors
- Reduce the time of the investment to the minimum. This rather simple rule has lots of implications, from logistics to legal conditions. Representatives of the investors, who are desirably financiers or businessmen but not attorneys-at-law, can pool investor funds into an account under the representatives’ control and verify the parties’ consents and willingness to proceed.
- Have all the transaction (key) terms agreed upon before the financing takes place. The investor or his representative must ascertain that the parties are in full agreement on all (key) terms of the transaction. While the parties might not be able to bear the cost of all agreements drafting before the transaction financing takes place, they can surely produce a complete term sheet for each agreement needed for the transaction. Any party receiving the transaction financing can also take the commitment toward the investor that no other additional or new (key) term shall be required from the other party after the financing takes place, preventing thereby the classic last minute requirement that makes the transaction fail.
The contracting parties program the contractual terms, payments to be made and all dispatches of documents used for the execution of the contract in the software application and may no longer retract their commitments. Once launched, the application performs the scheduled operations without human intervention, as scheduled.
End clients interact with a smart contract through transactions. Such transactions with a smart contract can invoke other smart contracts. These transactions might result in changing the state and sending financial assets from one smart contract to another or from one account to another. Financial assets can include nationally denominated currencies, cryptocurrencies, virtual stock certificates, or other assets whose value can be defined digitally.
Similar to a transfer of value on a blockchain, deployment of a smart contract on a blockchain occurs by sending a transaction from a wallet for the blockchain. The transaction includes the compiled code for the smart contract as well as a special receiver address. That transaction must then be included in a block that is added to the blockchain, at which point the smart contract’s code will execute to establish the initial state of the smart contract. Byzantine fault-tolerant algorithms secure the smart contract in a decentralized way from attempts to tamper with it. Once a smart contract is deployed, it cannot be updated. Smart contracts on a blockchain can store arbitrary state and execute arbitrary computations.
The reliability of the intelligent contract can be greatly increased by relying on a decentralized IT environment allowing secure access to the contractors and unfalsifiable by them.
Each smart contract may include information about the investment in the security. Such information may include the amount of the investment, the agreed-upon payouts, the revenue stream, the time the investment is agreed upon, the identities of the parties, etc. Investment information may further include conditional outcomes based upon each potential outcome, including the facilitation of payment from the investor to the seller, and/or the return of funds in event of a void or cancellation. In some embodiments, a settlement service may be agreed upon between the parties.
Some embodiments provide that the smart contracts may be generated on individual PC’s, on a mobile device and/or in the cloud. Such examples are non-limiting as the smart contracts may be generated at a variety of other devices and/or types thereof. In some embodiments, each smart contract may involve external services at the discretion of the parties. In some embodiments, a range of options may be selected by the parties at the time the smart contract is generated.
Some embodiments provide that a smart contract may be registered with a settlement service provider that is agreed to by the parties. In some embodiments, a settlement service may provide information about the outcome of the assets on which the security is based. In some embodiments, the settlement service may send the information to the counterparties, which may trigger the payouts under the terms of the smart contract. For example, the settlement service provider may initiate a bank transfer from the buyer to the seller based on the smart contract. In some embodiments, the process may be automated by software on a computer and/or server controlled by the settlement service. Embodiments herein do not require the funds to be held in any kind of escrow, however, such option is contemplated by this disclosure. For example, embodiments herein are directed to any financial settlement process that may be used in conjunction with the smart contracts as disclosed herein.
Some embodiments provide that the settlement transaction may be stored in blockchain to close the contract. In some embodiments, details corresponding to the settlement transaction may be retained for auditing, later scrutiny and/or to ensure that no errors are made.
FIG. 3 depicts a computer system 300 according to an embodiment of the present disclosure. In general, the computer system 300 may include a computing device 310, such as a special-purpose computer designed and implemented for receiving user inputs, determining and directing and controlling the output of signals. The computing device 310 may be or include data sources, client devices, and so forth. In certain aspects, the computing device 310 may be implemented using hardware or a combination of software and hardware. The computing device 310 may be a standalone device, a device integrated into another entity or device, a platform distributed across multiple entities, or a virtualized device executing in a virtualization environment.
The computing device 310 may communicate across a network 302. The network 302 may include any data network(s) or internetwork(s) suitable for communicating data and control information among participants in the computer system 300. This may include public networks such as the Internet, private networks, and telecommunications networks such as the Public Switched Telephone Network or cellular networks using cellular technology and/or other technologies, as well as any of a variety other local area networks or enterprise networks, along with any switches, routers, hubs, gateways, and the like that might be used to carry data among participants in the computer system 300. The network 302 may also include a combination of data networks and need not be limited to a strictly public or private network.
The computing device 310 may communicate with an external device 304. The external device 304 may be any computer, mobile device such as a cell phone, tablet, smart watch or other remote resource that connects to the computing device 310 through the network 302. This may include any of the servers or data sources described herein, including servers, content providers, databases or other sources for shot information to be used by the devices as described herein.
In general, the computing device 310 may include a controller or processor 312, a memory 314, a network interface 316, a data store 318, and one or more input/output interfaces 320. The computing device 310 may further include or be in communication with peripherals 322 and other external input/output devices that might connect to the input/output interfaces 320.
The controller 312 may be implemented in software, hardware or a combination of software and hardware. According to one aspect, the controller 312 may be implemented in application software running on a computer platform. Alternatively, the controller 312 may include a processor or other processing circuitry capable of processing instructions for execution within the computing device 310 or computer system 300. The controller 312, as hardware, may include a single-threaded processor, a multi-threaded processor, a multi-core processor and so forth. The controller 312 may be capable of processing instructions stored in the memory 314 or the data store 318.
The memory 314 may store information within the computing device 310. The memory 314 may include any volatile or non-volatile memory or other computer-readable medium, including without limitation a Random-Access Memory (RAM), a flash memory, a Read Only Memory (ROM), a Programmable Read-only Memory (PROM), an Erasable PROM (EPROM), registers, and so forth. The memory 314 may store program instructions, program data, executables, and other software and data useful for controlling operation of the computing device 310 and configuring the computing device 310 to perform functions for a user 330. The memory 314 may include a number of different stages and types of memory for different aspects of operation of the computing device 310. For example, a processor may include on-board memory and/or cache for faster access to certain data or instructions, and a separate, main memory or the like may be included to expand memory capacity as desired. All such memory types may be a part of the memory 314 as contemplated herein.
The memory 314 may, in general, include a non-volatile computer readable medium containing computer code that, when executed by the computing device 310 creates an execution environment for a computer program in question, e.g., code that constitutes processor firmware, a protocol stack, a database management system, an operating system, or a combination of the foregoing, and that performs some or all of the steps set forth in the various flow charts and other algorithmic descriptions set forth herein. While a single memory 314 is depicted, it will be understood that any number of memories may be usefully incorporated into the computing device 310.
The network interface 316 may include any hardware and/or software for connecting the computing device 310 in a communicating relationship with other resources through the network 302. This may include remote resources accessible through the Internet, as well as local resources available using short range communications protocols using, e.g., physical connections (e.g., Ethernet), radio frequency communications (e.g., Wi-Fi, Bluetooth), optical communications (e.g., fiber optics, infrared, or the like), ultrasonic communications, or any combination of these or other media that might be used to carry data between the computing device 310 and other devices. The network interface 316 may, for example, include a router, a modem, a network card, an infrared transceiver, a radio frequency (RF) transceiver for receiving AM/FM or satellite radio sources, a near field communications interface, a radio-frequency identification (RFID) tag reader, or any other data reading or writing resource or the like.
The network interface 316 may include any combination of hardware and software suitable for coupling the components of the computing device 310 to other computing or communications resources. By way of example and not limitation, this may include electronics for a wired or wireless Ethernet connection operating according to the IEEE 802.11 standard (or any variation thereof), or any other short or long range wireless networking components or the like. This may include hardware for short range data communications such as Bluetooth or an infrared transceiver, which may be used to couple to other local devices, or to connect to a local area network or the like that is in turn coupled to a data network 302 such as the Internet. This may also include hardware/software for a WiMax connection or a cellular network connection (using, e.g., CDMA, GSM, LTE, or any other suitable protocol or combination of protocols). The network interface 316 may be included as part of the input/output devices 320 or vice-versa.
The data store 318 may be any internal or external memory store providing a computer-readable medium such as a disk drive, an optical drive, a magnetic drive, a flash drive, or other device capable of providing mass storage for the computing device 310. The data store 318 may store computer readable instructions, data structures, program modules, and other data for the computing device 310 or computer system 300 in a non-volatile form for relatively long-term, persistent storage and subsequent retrieval and use. For example, the data store 318 may store an operating system, application programs, program data, databases, files, and other program modules or other software objects and the like.
As used herein, processor, microprocessor, and/or digital processor may include any type of digital processing device such as, without limitation, digital signal processors (“DSPs”), reduced instruction set computers (“RISC”), complex instruction set computers (“CISC”) processors, microprocessors, gate arrays (e.g., field programmable gate arrays (“FPGAs”)), programmable logic device (“PLDs”), reconfigurable computer fabrics (“RCFs”), array processors, secure microprocessors, and application-specific integrated circuits (“ASICs”). Such digital processors may be contained on a single unitary integrated circuit die or distributed across multiple components.
As used herein, computer program and/or software may include any sequence or human or machine cognizable steps which perform a function. Such computer program and/or software may be rendered in any programming language or environment including, for example, C/C++, C#, Fortran, COBOL, MATLAB™, PASCAL, GO, RUST, SCALA, Python, assembly language, markup languages (e.g., HTML, SGML, XML, VoXML), and the like, as well as object-oriented environments such as the Common Object Request Broker Architecture (“CORBA”), JAVA™ (including J2ME, Java Beans, etc.), Binary Runtime Environment (e.g., “BREW”), and the like.
The input/output interface 320 may support input from and output to other devices that might couple to the computing device 310. This may, for example, include serial ports (e.g., RS-232 ports), universal serial bus (USB) ports, optical ports, Ethernet ports, telephone ports, audio jacks, component audio/video inputs, HDMI ports, and so forth, any of which might be used to form wired connections to other local devices. This may also include an infrared interface, RF interface, magnetic card reader, or other input/output system for wirelessly coupling in a communicating relationship with other local devices. It will be understood that, while the network interface 316 for network communications is described separately from the input/output interface 320 for local device communications, these two interfaces may be the same, or may share functionality, such as where a USB port 370 is used to attach to a Wi-Fi accessory, or where an Ethernet connection is used to couple to a local network attached storage. The input/output interface 320 may further output signals to displays of peripheral devices, as described herein.
As used herein, a user 330 is any human that interacts with the computer system 300. In this context, a user may be generally classed within one of two categories. One category is an administrator of the system, representing the seller and/or financial institution organizing and conducting the offering of the security. Another category is an investor who buys and sells shares in the security.
In certain embodiments the I/O interface 320 facilitates communication with input and output devices for interacting with a user. For example, the I/O interface may communicate with one or more devices such as a user-input device and/or a display 350 which may be instantiated on the device described herein or on a separate device such as a mobile device 208, which enable a user to interact directly with the controller 312 via bus 332. The user-input device may comprise one or more push-buttons, a touch screen, or other devices that allows a user to input information. In these embodiments, the computer system may further comprise a display to provide visual output to the user. The display may comprise any of a variety of visual displays, such as a viewable screen, a set of viewable symbols or numbers, and so on. One can appreciate that the inputs and outputs of the computer system would be different for administrators and investors. Accordingly, the computing device 310 may communicate with administrators and investors with different interfaces 324 and 328.
A peripheral 322 may include any device used to provide information to or receive information from the computing device 310. This may include human input/output (I/O) devices such as a keyboard, a mouse, a mouse pad, a track ball, a joystick, a microphone, a foot pedal, a camera, a touch screen, a scanner, or other device that might be employed by the user 330 to provide input to the computing device 310. This may also or instead include a display, a printer, a projector, a headset or any other audiovisual device for presenting information to a user. The peripheral 322 may also or instead include a digital signal processing device, an actuator, or other device to support control of or communication with other devices or components. In one aspect, the peripheral 322 may serve as the network interface 316, such as with a USB device configured to provide communications via short range (e.g., Bluetooth, Wi-Fi, Infrared, RF, or the like) or long range (e.g., cellular data or WiMax) communications protocols. In another aspect, the peripheral 322 may augment operation of the computing device 310 with additional functions or features, or other device. In another aspect, the peripheral 322 may include a storage device such as a flash card, USB drive, or other solid-state device, or an optical drive, a magnetic drive, a disk drive, or other device or combination of devices suitable for bulk storage. More generally, any device or combination of devices suitable for use with the computing device 310 may be used as a peripheral 322 as contemplated herein.
Other hardware 326 may be incorporated into the computing device 310 such as a coprocessor, a digital signal processing system, a math co-processor, a graphics engine, a video driver, a camera, a microphone, additional speakers, and so forth. The other hardware 326 may also or instead include expanded input/output ports, extra memory, additional drives, and so forth.
A bus 332 or combination of busses may serve as an electromechanical backbone for interconnecting components of the computing device 310 such as the controller 312, memory 314, network interface 316, other hardware 326, data store 318, and input/output interface. As shown in the figure, each of the components of the computing device 310 may be interconnected using a system bus 332 in a communicating relationship for sharing controls, commands, data, power, and so forth.
The computing device 310 is connected to a power source 360 to provide electrical power for the computing device to run.
The various illustrative logical blocks, modules and circuits described in connection with the present disclosure may be implemented or performed with a processor specially configured to perform the functions discussed in the present disclosure. The processor may be a neural network processor, a digital signal processor (DSP), an application specific integrated circuit (ASIC), a field programmable gate array signal (FPGA) or other programmable logic device (PLD), discrete gate or transistor logic, discrete hardware components or any combination thereof designed to perform the functions described herein. Alternatively, the processing system may comprise one or more neuromorphic processors for implementing the neuron models and models of neural systems described herein. The processor may be a microprocessor, controller, microcontroller, or state machine specially configured as described herein. A processor may also be implemented as a combination of computing devices, e.g., a combination of a DSP and a microprocessor, a plurality of microprocessors, one or more microprocessors in conjunction with a DSP core, or such other special configuration, as described herein.
The steps of a method or algorithm described in connection with the present disclosure may be embodied directly in hardware, in a software module executed by a processor, or in a combination of the two. A software module may reside in storage or machine readable medium, including random access memory (RAM), read only memory (ROM), flash memory, erasable programmable read-only memory (EPROM), electrically erasable programmable read-only memory (EEPROM), registers, a hard disk, a removable disk, a CD-ROM or other optical disk storage, magnetic disk storage or other magnetic storage devices, or any other medium that can be used to carry or store desired program code in the form of instructions or data structures and that can be accessed by a computer. A software module may comprise a single instruction, or many instructions, and may be distributed over several different code segments, among different programs, and across multiple storage media. A storage medium may be coupled to a processor such that the processor can read information from, and write information to, the storage medium. In the alternative, the storage medium may be integral to the processor.
The methods disclosed herein comprise one or more steps or actions for achieving the described method. The method steps and/or actions may be interchanged with one another without departing from the scope of the claims. In other words, unless a specific order of steps or actions is specified, the order and/or use of specific steps and/or actions may be modified without departing from the scope of the claims.
The functions described may be implemented in hardware, software, firmware, or any combination thereof. If implemented in hardware, an example hardware configuration may comprise a processing system in a device. The processing system may be implemented with a bus architecture. The bus may include any number of interconnecting buses and bridges depending on the specific application of the processing system and the overall design constraints. The bus may link together various circuits including a processor, machine-readable media, and a bus interface. The bus interface may be used to connect a network adapter, among other things, to the processing system via the bus. The network adapter may be used to implement signal processing functions. For certain aspects, a user interface (e.g., keypad, display, mouse, joystick, etc.) may also be connected to the bus. The bus may also link various other circuits such as timing sources, peripherals, voltage regulators, power management circuits, and the like, which are well known in the art, and therefore, will not be described any further.
The processor may be responsible for managing the bus and processing, including the execution of software stored on the machine-readable media. Software shall be construed to mean instructions, data, or any combination thereof, whether referred to as software, firmware, middleware, microcode, hardware description language, or otherwise.
In a hardware implementation, the machine-readable media may be part of the processing system separate from the processor. However, as those skilled in the art will readily appreciate, the machine-readable media, or any portion thereof, may be external to the processing system. By way of example, the machine-readable media may include a transmission line, a carrier wave modulated by data, and/or a computer product separate from the device, all which may be accessed by the processor through the bus interface. Alternatively, or in addition, the machine-readable media, or any portion thereof, may be integrated into the processor, such as the case may be with cache and/or specialized register files. Although the various components discussed may be described as having a specific location, such as a local component, they may also be configured in various ways, such as certain components being configured as part of a distributed computing system.
The machine-readable media may comprise a number of software modules. The software modules may include a transmission module and a receiving module. Each software module may reside in a single storage device or be distributed across multiple storage devices. By way of example, a software module may be loaded into RAM from a hard drive when a triggering event occurs. During execution of the software module, the processor may load some of the instructions into cache to increase access speed. One or more cache lines may then be loaded into a special purpose register file for execution by the processor. When referring to the functionality of a software module below, it will be understood that such functionality is implemented by the processor when executing instructions from that software module. Furthermore, it should be appreciated that aspects of the present disclosure result in improvements to the functioning of the processor, computer, machine, or other system implementing such aspects.
If implemented in software, the functions may be stored or transmitted over as one or more instructions or code on a computer-readable medium. Computer-readable media include both computer storage media and communication media including any storage medium that facilitates transfer of a computer program from one place to another.
Further, it should be appreciated that modules and/or other appropriate means for performing the methods and techniques described herein can be downloaded and/or otherwise obtained by a user terminal and/or base station as applicable. For example, such a device can be coupled to a server to facilitate the transfer of means for performing the methods described herein. Alternatively, various methods described herein can be provided via storage means, such that a user terminal and/or base station can obtain the various methods upon coupling or providing the storage means to the device. Moreover, any other suitable technique for providing the methods and techniques described herein to a device can be utilized.
The computer program controls input and operation of the device. The computer program includes at least one code segment stored in or on a computer-readable medium residing on or accessible by the device for instructing the computing elements, and any other related components to operate in the manner described herein. The computer program is preferably stored within the memory and comprises an ordered listing of executable instructions for implementing logical functions in the device. However, the computer program may comprise programs and methods for implementing functions in the device that are not an ordered listing, such as hard-wired electronic components, programmable logic such as field-programmable gate arrays (FPGAs), application specific integrated circuits, or other similar or conventional methods for controlling the operation of electrical or other computing devices.
Similarly, the computer program may be embodied in any computer-readable medium for use by or in connection with an instruction execution system, apparatus, or device, such as a computer-based system, processor-containing system, or other system that can fetch the instructions from the instruction execution system, apparatus, or device, and execute the instructions. The computer-readable medium may even be paper or another suitable medium upon which the program is printed, as the program can be electronically captured, via for instance, optical scanning of the paper or other medium, then compiled, interpreted, or otherwise processed in a suitable manner, if necessary, and then stored in a computer memory.
Figure 4 shows a process flow diagram 400 for defining and offering securities for sale by the incubator company 110 according to an embodiment of the disclosed subject matter.
The process flow diagram 400 starts at block 402 wherein the computer system receives inputs from administrator(s) representing the seller (e.g. company 100 and incubator 110) regarding a venture capitalization effort such as an IPO to be offered as described herein. Inputs include a target amount of capital to be raised, information regarding company 100’s current and potential valuation, etc.
The computer system determines a structure for the security in block 404. The determination of the structure comprises conducting activities in blocks 221, 222 and 223 of Figure 2B. It is to be appreciated that defining the structure of the offering in block 404 may comprise several iterative interactions between the computer system and administrator(s) or seller(s) to define the final structure of the security (arrow 406a).
Once the structure of the offering is determined, the computer system moves to executing the offering (block 251 of Figure 2B) by moving to block 406. Block 406 comprises offering the security for sale to potential investors. Block 408 comprises receiving “bids” for shares from investors. As discussed above, in some embodiments, a “bid” may comprise a potential buyer expressing interest in purchasing shares of the security in response to pre-sale information disclosures provided by the seller and/or incubator, such as in roadshows, or queries about the security which is not currently offered for sale. In embodiments wherein an investor expresses interest or initiates a query, the expressed interest or query is directed by the system from the investor into block 402 of the process flow scheme (arrow 408a) for analysis and response from the seller(s). It is to be appreciated that defining the structure of the security in block 404 based on buyer-initiated inputs may comprise several iterative interactions among the computer system, investors and administrator(s) or seller(s) (arrows 406a and 408a) to define the final structure of the security. “Bids” also refers to offers to purchase shares of the security by one or more investors after the final structure of the security is defined.
Block 410 comprises accepting the bids from investors. Accepting the bids includes issuing shares to the investors at their bid price(s) and holding them in the computer system. As described above, acceptance of the bids by sellers may comprise generation of a smart contract that defines the final terms and conditions of the security.
The system tracks the sales of securities in block 412, including the total number of securities sold, the prices offered in bids and accepted by the computer system and the holders of the securities. The computer system tracks revenues associated with the sale of the securities and determines whether targets defined in the security have been met in block 414. Targets may include revenue from sales, performance targets, etc.
If the computer system determines that the target(s) are reached in block 414, the computer system moves to block 418 and disperses payments to parties based on the terms of the securities. Payments may include payments to the incubator company for managing the offering, payments to the seller (company 100) representing the venture capital desired to be raised, and investors desiring to exit the trade as described above.
The system and methods described herein may be used for private offerings, initial public offerings or combinations thereof. For example, securities may be offered to a limited number of private venture capital entities.
Claims
- A system for financing a venture comprising an incubator financial firm configured to manage activities related to raising funds for the venture against an equity participation and a put option on this equity participation to the issuer; and a special vehicle firm that holds substantially all assets of the entity seeking financing; wherein the incubator financial firm defines an investor offering to raise funds from investors against a share of the capital prior to the IPO and a pro rata share of the raised funds payable after the IPO.
- A company for financing a venture comprising a financial firm configured to manage activities related to raising funds for the venture against an equity participation and a put option on this equity participation to the issuer.
- The company of claim 2 wherein the financial firm defines an investor offering to raise funds from investors against a share of the capital prior to the IPO and a pro rata share of the raised funds payable after the IPO.
- A method for financing a venture comprising establishing an incubator financial firm configured to manage activities related to raising funds for the venture against an equity participation and a put option on this equity participation to the issuer, wherein the incubator financial firm defines an investor offering to raise funds from investors against a share of the capital prior to the IPO and a pro rata share of the raised funds payable after the IPO; and establishing a special vehicle firm that holds all assets of the entity seeking financing.
- A method for providing an equity security, the method comprising:
- defining an offering for sale of investment shares in a venture;
- receiving bids from investors for purchase of the investment shares;
- accepting the bids from investors;
- tracking revenue associated with the sale of the investment shares; and
- paying parties a portion of the revenue as it is received.
- A system comprising a computerized system with hardware and specialized software components for developing, executing and administering sale of securities, the system comprising a non-transitory computer readable storage medium comprising a plurality of computer readable instructions embodied thereon which, when executed by the computerized system, causes the computerized system to:
- define an offering for sale of investment shares in a venture;
- receive bids from investors for purchase of the investment shares;
- accept the bids from investors;
- track revenue associated with the sale of the investment shares; and
- pay parties a portion of the revenue as it is received.
- A non-transitory computer readable storage medium comprising a plurality of computer readable instructions embodied thereon wherein the instructions, when executed by a computerized system with hardware and specialized software components for developing, executing and administering intellectual property securities, cause the computerized system to:
- define an offering for sale of investment shares in a venture;
- receive bids from investors for purchase of the investment shares;
- accept the bids from investors;
- track revenue associated with the sale of the investment shares; and
- pay parties a portion of the revenue as it is received.
Abstract
A computerized system with hardware and specialized software components for developing, executing and administering sale of securities for raising venture capital by an incubator financing company.